Wi-Fi devices share the same medium, RF. In order to avoid collisions with other devices connected to the same AP and those nearby, all devices use a form of contention called Carrier Sense Multiple Access with Collision Avoidance (CSMA/CA). The 802.11-2016 standard defines Distributed Coordination Function (DCF) as the process devices must follow in order to share access to the medium. This process has been used through each standard since the original 802.11-1997 with the most notable improvements being added in 802.11e-2005.
The information covered in this post is expected knowledge in all wireless exams. Understanding the medium access methods that devices follow is the foundation of Wi-Fi. These concepts extend further than my descriptions; be sure to read the study guide for the exam you may be preparing for and the latest version of the 802-11 standard (of course) for full detail. Those reading this to study for CWNA or CWAP can cross off the objectives mentioned below.
CWNA-107 Objectives covered:
- 3.5 Explain 802.11 channel access methods
- 3.5.1 DCF
- 3.5.2 EDCA
- 3.5.3 RTS/CTS
- 3.5.4 CTS-to-Self
- 3.5.5 NAV
- 3.5.6 Physical carrier sense and virtual carrier sense
CWAP-403 Objectives covered:
- 5.1 Understand 802.11 contention algorithms in-depth and know how they impact WLANs
- 5.1.1 Distributed Coordination Function (DCF)
- Carrier Sense and Energy Detect
- Network Allocation Vector (NAV)
- Contention Window (CW) and random back-off
- Interframe Spacing
- 5.1.2 Enhanced Distributed Channel Access (EDCA)
- EDCA Function (EDCAF)
- Access Categories and Queues
- AIFSN
- 5.1.1 Distributed Coordination Function (DCF)
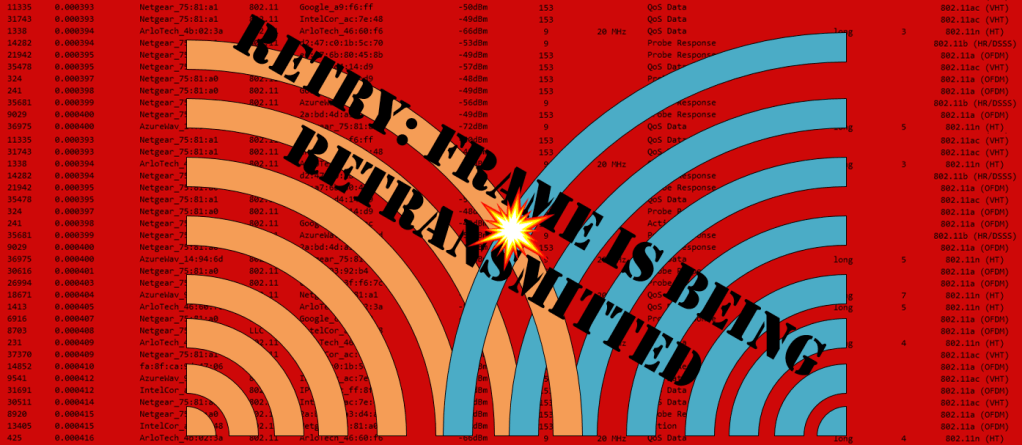
CSMA/CA in Operation
In Wi-Fi, not considering any multi-user transmissions, devices take turns sending one at a time. While one device transmits, all the others listen, even if the frame is not destined for the listeners. This concept comes from the use of Carrier Sense Multiple Access with Collision Avoidance (CSMA/CA). After the transmitting device is done sending data, all devices that wish to transmit will follow a similar process. It involves waiting a calculated random amount of time and checking to see if other devices are transmitting. If they aren’t, that device will request control of the medium and begin transmitting. If other stations are transmitting, the device will set a timer for itself based on the duration of the transmission from the other device. This simplified process is followed for every frame transmission to ensure that every device gets equal opportunity to transmit. This equal opportunity is the “multiple access” part of CSMA/CA. Carrier sense involves devices checking whether the wireless medium is busy or idle. These processes are what make up CSMA/CA.
Distributed Coordination Function (DCF)
DCF is the process by which CSMA/CA is applied to Wi-Fi networks and can be found in the 802.11-1997 standard. DCF defines four components to ensure devices share the medium equally: Physical Carrier Sense, Virtual Carrier Sense, Random Back-off timers, and Interframe Spaces (IFS). DCF is used in non-QoS WLANs.
Physical Carrier Sense
Physical Carrier Sense is the process of a device checking the frequency to determine whether the medium is in use or not. This process can be thought of as a constant state for the device unless it is the one who is transmitting or receiving frames. Devices use physical carrier sense to detect an incoming signal and attempt to synchronize with it. Recall that the device will apply a PHY header and preamble to each frame; the preamble starts with a stream of 0s and 1s. This stream is what devices are listening for when performing physical carrier sense. Prior to transmitting frames on the medium, a station will perform physical carrier sense after waiting for its random back-off timer to verify the medium is clear. Devices perform physical carrier sense as part of the clear channel assessment (CCA) process.
Clear Channel Assessment (CCA)
Devices use two methods to determine whether the channel is clear. One is used to detect other Wi-Fi transmissions, signal detect (SD), and the other is used to detect any sources of interference that are affecting the medium, energy detect (ED).
Signal detect – Device detects an 802.11 preamble in range. The threshold is a signal that is about 4dB above the noise floor. This means that the device will defer transmissions if a nearby device is starting to transmit.
Energy detect – Device listens for any energy in the medium that is 20dB above the signal detect value. These devices could be Bluetooth, microwaves, baby monitors, or any other device that primarily operates in 2.4GHz or causes interference in the 2.4GHz range as a byproduct to its primary function.
The flowchart below represents a simplified version of the CCA process.

The result of both tests is either busy or idle. The station performing CCA will only transmit if both tests result in idle. When signal detect results in busy, the station will synchronize and begin to receive the transmission. Energy detect busy means there is a high level of interference nearby; in this case, the station will defer one slot time then perform CCA again. The CCA process takes ~4 microseconds to complete.
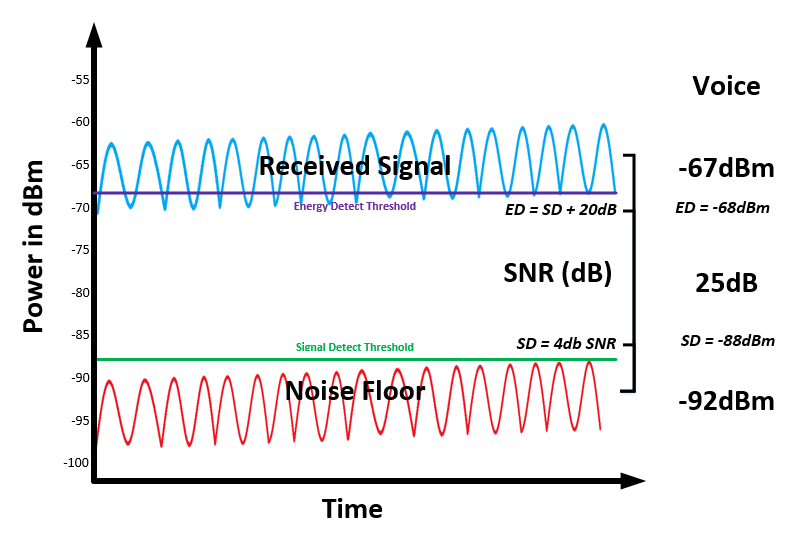
In RF heavy environments where 2.4GHz is relied on, and other 2.4GHz protocols are in use (such as Bluetooth or Zigbee), we can begin to understand one of the reasons why Wi-Fi can easily be perceived as slow or unreliable. In RF heavy areas with a high noise floor, the signal and energy detect thresholds will increase while the received signal strength (RSSI) remains the same. This difference allows devices to view the energy detect result as idle in noisier environments. If these values were not based on the noise floor, interferes would have a much larger impact than they already do.
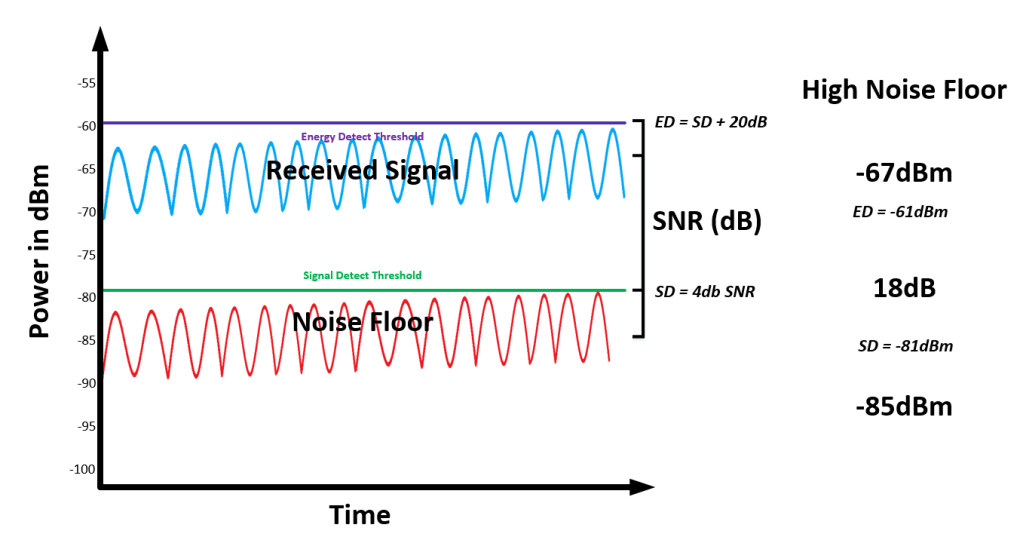
Most devices will prefer to connect via 5GHz, but there are many cases where 2.4GHz is still necessary. Disabling 2.4GHz radios on certain APs (then validating coverage) and performing spectrum analysis are key when troubleshooting. There is no place to check that a device performed energy detect and it failed 30 times. There is, however, a way to view layer 1, identify sources of interference, and tune your wireless network around them.
Adjacent Channel Interference
Devices that are connected to a neighbor AP will likely be using a different frequency which will not be detectable. In 2.4GHz however, you may find the use of the overlapping channels. These are channels other than 1, 6, and 11. This results in adjacent channel interference; because these channels partially overlap with others, stations will be able to interpret frames sent by devices connected to other APs. This results in devices unnecessarily deferring transmissions.
Virtual Carrier Sense
Virtual carrier sense is a secondary process used to avoid collisions on the wireless medium. When a station transmits an 802.11 frame, it includes a value in the Duration/ID field of the frame’s header. As we know from the physical carrier sense process, when a station hears another device transmitting, it will synchronize its radio with that transmission to receive the frame. After decoding the 0s and 1s sent across the air, the station will see the Duration/ID field value and set a timer known as the network allocation vector (NAV). The duration set by a station is the amount of time, in microseconds, that it will take to send the frame(s), wait the appropriate IFS, and receive an ACK. The listening station will not contend for the medium again until it counts down and reaches a NAV of 0. Virtual carrier sense works together with physical carrier sense; stations perform both processes for each transmission it wishes to send, and all frames heard from others. It is important to understand what response a station is expecting, if any, for each frame sent. Both acknowledgement (ACK) and beacons frames use a 0-duration value to indicate that, after receiving, the airtime is no longer in use and can once again be contended for.
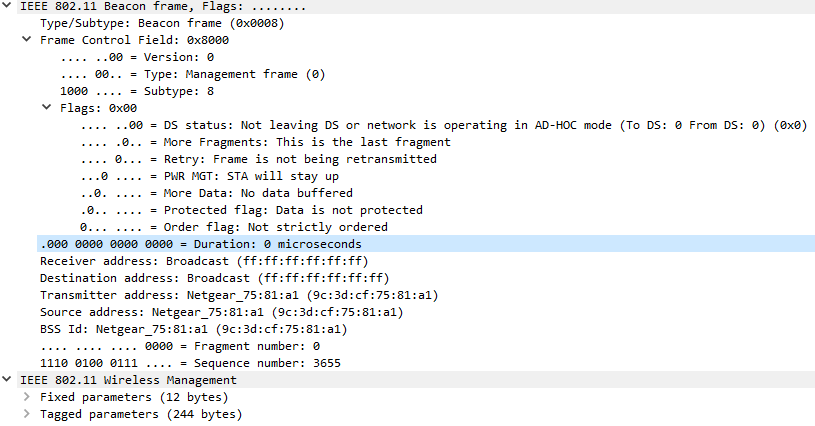
When a station detects that the medium is idle and has waiting the appropriate amount of time, it will send a request to send (RTS) frame, wait for a clear to send (CTS) frame response from the AP, then transmit one frame. For now, know that the duration in the RTS frame is the full amount of time the station wishes to “reserve” the medium for. Until receiving a clear to send (CTS) from the AP, the medium is not yet reserved. More on the RTS and CTS process later. The station is only permitted to transmit one frame due unless the traffic sent is part of the voice or video access categories (AC_VO and AC_VI) which have TXOP ≠ 0.
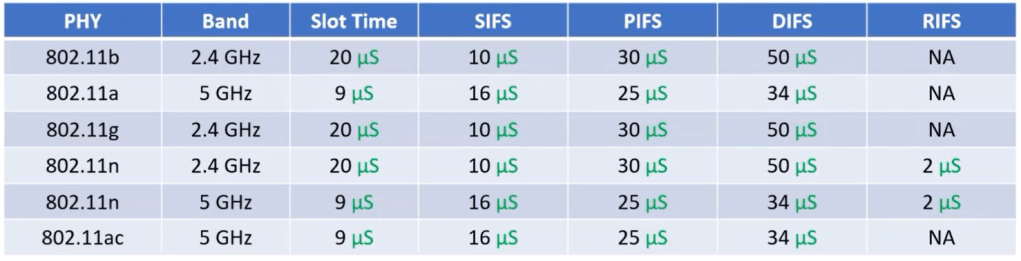
Pseudo-Random Back-off Timer
Following the physical and virtual carrier sense procedures, when all stations have counted down their NAV timers from the previous transmission, each device chooses a random amount of time, perform the CCA process once last time and, if idle/idle, begin to transmit. Each device chooses a random number in a range called the contention window (CW), this number is then multiplied by a slot time value. The slot time is statically set for each PHY; 802.11a/g/n/ac (OFDM) all use 9μs slot times. 802.11b radios use a 20μs slot time. 802.11e introduced QoS and defined the CW sizes per access category. This is known as the arbitration process. These window sizes and access categories are discussed in detail later.
The table below shows the pre-802.11e contention window size along with those that were introduced.
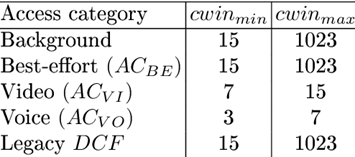
The CWmin value is the smallest max value used for the random number selection; the CWmax value is the largest max value used. When a collision does occur, the CWmin value is doubled and 1 is added. For example, if the first attempt to transmit a frame fails, the new CWmin would double from 15 and add 1, making the new CWmin 31. This results in the station selecting from a larger range of numbers. Each retry makes the station randomly select a number from a larger contention window. Assuming all networks primarily use 802.11n or newer devices, the slot time in use is 9μs.
The animation below shows three devices in a BSS contending for the medium, each of which are still using the lowest CWmin value. The number on the device indicates the value it randomly chose between 0 and 15. Each block represents 9μs. Because each device is using OFDM, the one that chooses the lowest CW value wins (0 is valid).
After counting down the slot times, the device will perform one last CCA before requesting control of the medium by sending an RTS frame. If the energy detect check results in busy, the device will wait one more slot time and perform another CCA. If another device in the BSS randomly chooses a smaller number, that device will transmit first. The other devices then update their NAV timers as part of the virtual carrier sense process. After their NAV timers reach 0, that device will continue counting down from the value it chose before. For example, in the mobile phone in the animation above will only count down 4 slot times after laptop #2 has transmitted its frames. Laptop #1 will only count down 2 slot times.
Interframe spaces (IFS)
Interframe spaces are periods of time between frames; they are used to allow frames to be processed in a timely manner, avoid interference by ensuring frames are received, and prioritize transmission of certain frames. IFS is defined in the 802.11-2007 standard as “The time from the end of the last symbol of the previous frame to the beginning of the first symbol of the preamble of the subsequent frame as seen at the air interface.” When a station has control of the medium, it exchanges frames with the receiver using SIFS. Controlling the exchange of frames and assisting in ordered processing is the goal of IFS. There are multiple types of IFS, some defined by the original standard and others added to in 802.11e-2005/802.11n-2009. The type of IFS is dependent on the frame that will come after it. Using a shorter duration IFS gives certain frames priority over others, such as an ACK frame using short IFS (SIFS). Similar to how all data frames in 802.11ac are sent as QoS data frames, all IFS in a QoS-BSS are sent as AIFS. BSS’ that do not support QoS will use the legacy DCF IFS (DIFS).
The figure below shows a frame exchange between two stations while a third uses virtual carrier sense to defer during the transmission.

By comparing the figures above and below, we see that IFS’ are used when a station has control of the medium as well as immediately after the medium is available for contention. Devices must wait for an IFS period before they begin the medium contention process. Subsequent transmissions, those after the RTS-CTS process, take place using SIFS to maintain control of the medium. This is how traffic gains priority, by its type, over contending devices when starting the contention process.

The actual amount of time for each IFS varies by type and network conditions. The CWNA exam expects you to know which frames use which IFS type. The CWAP exam expects you to know how the common IFS are calculated.
The priority order is as follows: RIFS > SIFS > PIFS > DIFS/AIFS > EIFS.
DIFS – DCF IFS – Duration is SIFS + 2 slot times. Used by standard data frames, giving data frames using SIFS priority.
SIFS – Short IFS – Shortest IFS prior to 802.11n. Duration of 16μs in 5GHz and 10μs in 2.4GHz. The IEEE explains the use of SIFS as “SIFS shall be used when STAs have seized the medium and need to keep it for the duration of the frame exchange sequence to be performed. Using the smallest gap between transmissions within the frame exchange sequence prevents other STAs, which are required to wait for the medium to be idle for a longer gap, from attempting to use the medium, thus giving priority to completion of the frame exchange sequence in progress.” Frames specified to use SIFS will take priority over those using shorter IFS. The figure above shows the 3 main uses of SIFS:
CTS frames sent as a response to RTS frames.
Data frames sent immediately after a CTS frame.
ACK frames sent immediately after receiving a data frame.
RIFS – Reduced IFS – Introduced in 802.11n for networks operating in Greenfield mode for burst transmissions. Shortest IFS at 2μs. 802.11ac and later standards do not use RIFS.
PIFS – Point IFS – Used to transition from DCF to Point Coordination Function (PCF) mode. Duration is SIFS + 1 slot time. Optional part of 802.11. Never implemented. PCF is not covered in this post.
AIFS – Arbitration IFS – Used in QoS networks for the transmission of all data, management, and select control frames. Described in detail below.
EIFS – Extended IFS – Used in legacy DCF networks when a station is retransmitting a frame that was previously corrupted due to collision or interference. All devices look for frames that have an incorrect frame check sequence (FCS), this is how they identify corrupt frames. When any AP or station hears a corrupt frame on their channel, they defer transmission for an EIFS to allow the frame to be retransmitted. To calculate the EIFS time, use the following formula:
EIFS = SIFS + (8 * ACKsize) + Preamble Length + PLCP Header Length + DIFS.
For OFDM, this equates to 160μs by default.
The table below shows the slot time and calculated IFS times for each PHY.
Near/Far
A side-effect to the EIFS deferral process is called near/far. When stations are near an AP, sending at high data rates, the devices further away can’t decode frames at that distance. The result is that, the far away device sees the frame as corrupt and waits an EIFS rather than a DIFS before beginning the contention process; the device then ends up in a cycle of not winning the medium.
Hybrid Coordination Function (HCF)
Defined by 802.11e-2005, Hybrid Coordination Function introduced two channel access methods, HCF Controlled Channel Access (HCCA) and Enhanced Distributed Channel Access (EDCA). HCCA improves on PCF while EDCA improves on DCF; both in an effort to make more efficient use of the medium. We will focus on EDCA since HCCA (based on PCF) is not used in the real world.
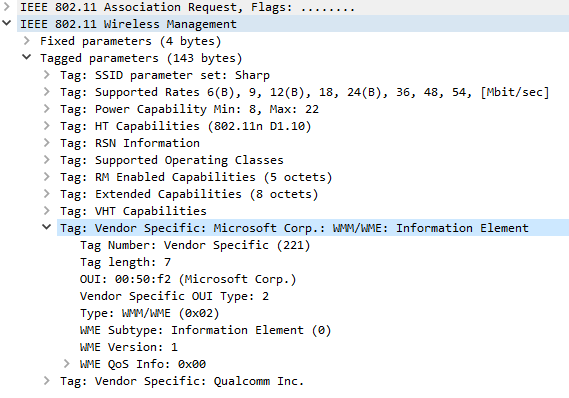
For devices to acquire the Wi-Fi Alliance certification for Wi-Fi Multimedia (WMM), they must support EDCA. Stations that do support 802.11e QoS protocols are called QoS stations; they can be identified by the WMM information element (IE) in probe request and association request frames.
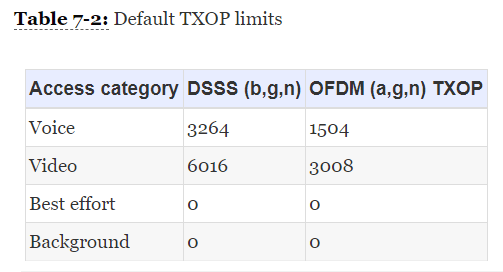
Within a QoS-BSS, the channel access is no longer equal for all devices. The four access categories allow for the prioritization of traffic base on type, they are: voice, video, best effort, and background. There are three major changes to the original 802.11 medium contention:
AIFS – DIFS is no longer used. All QoS STAs use AIFS.
Contention Window – Size varies for each access category.
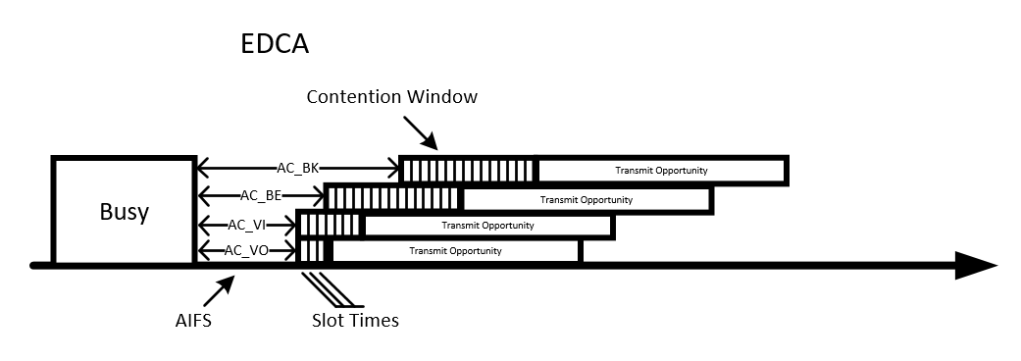
TXOP – voice and video access categories have a transmit opportunity (TXOP) that allow transmission of multiple frames, called a contention-free burst (CFB) for a specified duration within a single transmission period. The table below shows the default TXOP values.
For the Pseudo-Random Back-off Timer adjustment, AIFS gives a different slot time range for each category. Higher priority traffic, such as voice, have a lower number of slot times, making it more likely for that device to win access to the medium over lower categories. The table below shows the default values for each category, unique for each PHY. To calculate the AIFS length for each category, use the following formula:
AIFS = SIFS + (# of AC Slot Times * 9μs).
These AC slot times are found in the table below.
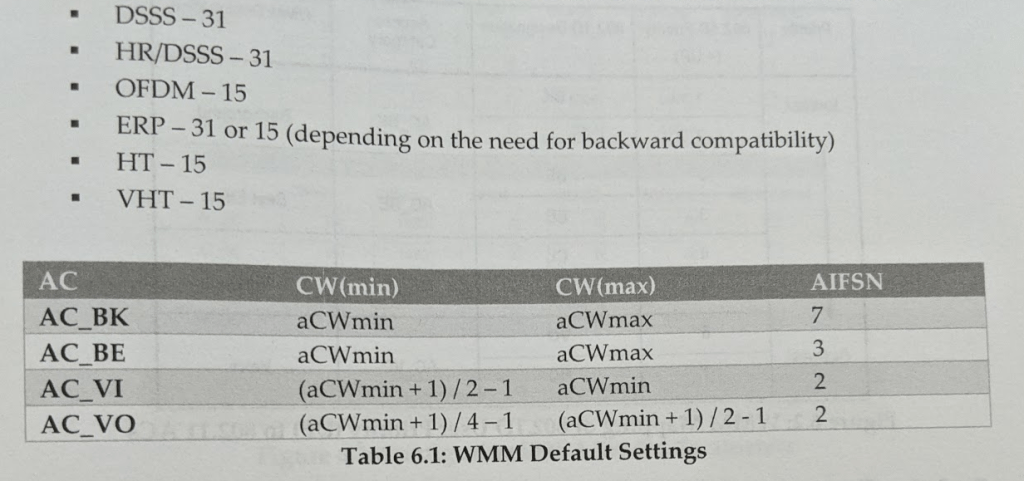
Calculating for 5GHz (OFDM), using the SIFS time of 16μs and slot time of 9μs, the results are below. Recall the DCF formula: DIFS = SIFS (9μs * 2). This results in a 34μs DIFS for OFDM transmissions.
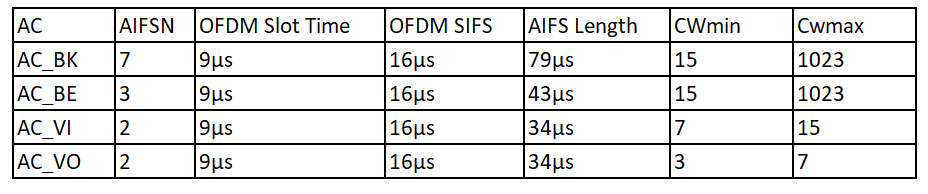
The image below shows the variable AIFS for each category and variable CWmin values for a transmission. You can see that voice and video categories have a smaller AIFS and much smaller contention window size. With these values, data traffic will win contention of the medium once for every two times that voice traffic wins.
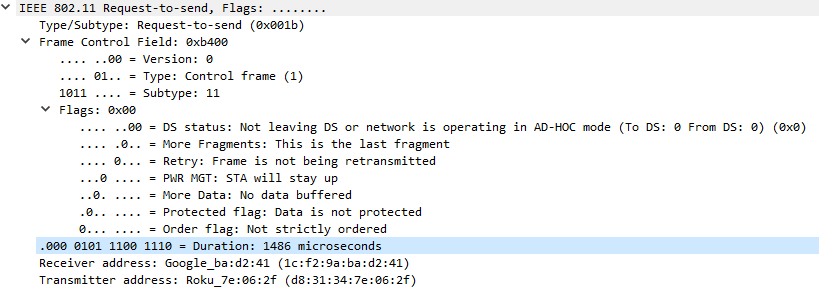
RTS-CTS Process
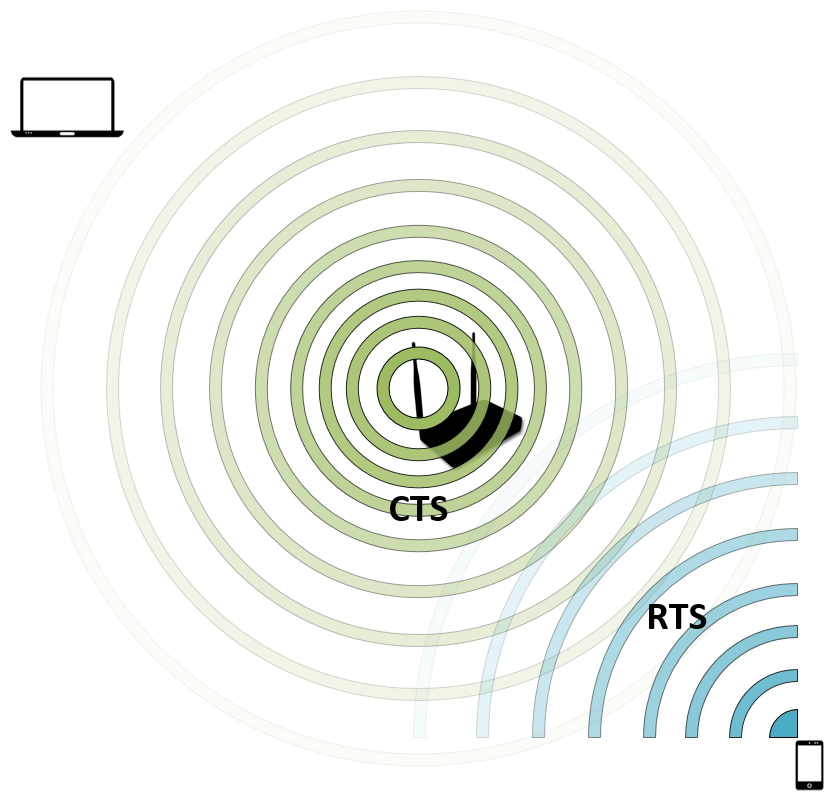
Request to send (RTS) and clear to send (CTS) frames are used before each data frame transmission and are key to the virtual carrier sense process. As mentioned earlier, when a station transmits a frame it will include a duration field. Stations nearby synchronize with this transmission, decode the frame, and update their NAV timers. The RTS-CTS process is a NAV distribution method. A station will send an RTS frame, requesting to reserve the medium for the amount of time listed in the duration, but stations far away may not be able to decode the frame (depending on their receive sensitivity) and not update their NAV timer. To resolve this issue, the CTS frame is used. CTS is a response from the AP, confirming medium reservation, which can be heard by all stations in the BSS.
The image below shows a mobile phone sending an RTS frame and the AP responding with a CTS frame. The laptop was unable to decode the RTS but can decode the CTS sent by the AP.
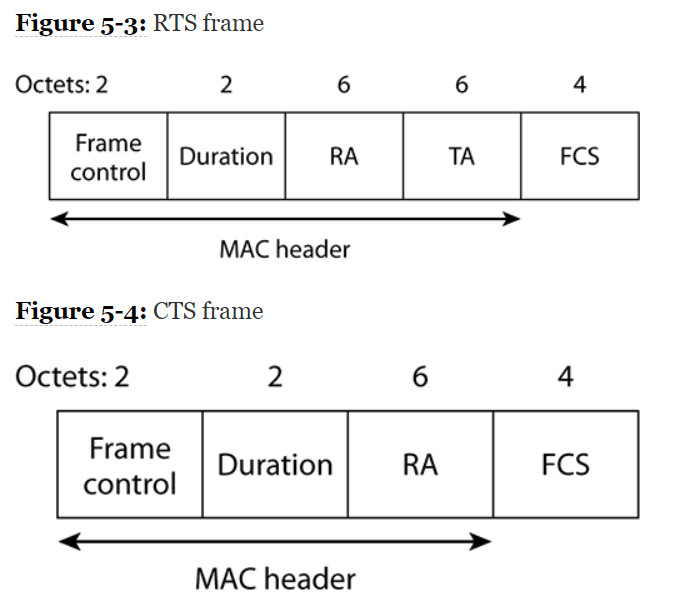
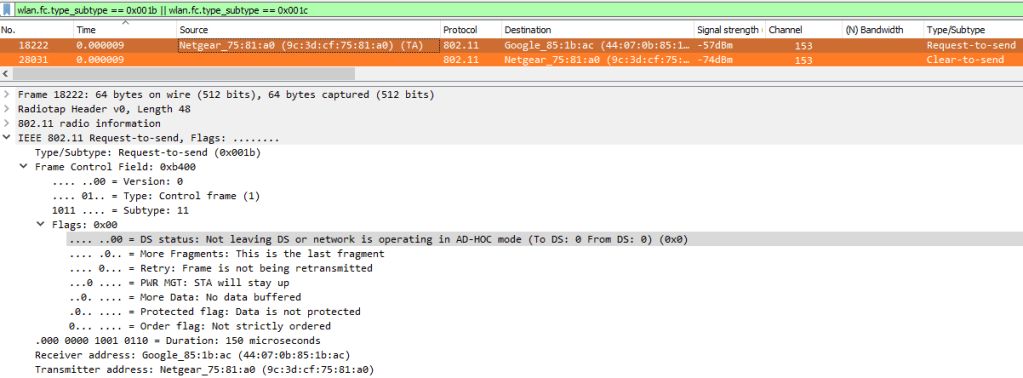
The format of these frames is simple. The RTS frame contains the full duration of the frame exchange along with the receiver address (RA) being the intended recipient of the transmission and the transmitter address (TA) being the address of the station sending the frame. The CTS frame contains the original duration, minus the amount of time spent transmitting the RTS and one SIFS, back to the original transmitter using its MAC address in the RA field. For exams, be sure to know which, and how many, of the address fields are used.
The figures below show the fields used in the frame header for both CTS and RTS frames.
The following Wireshark filter can be used to view RTS and CTS frames:
wlan.fc.type_subtype == 0x001b || wlan.fc.type_subtype == 0x001c
CTS-to-Self
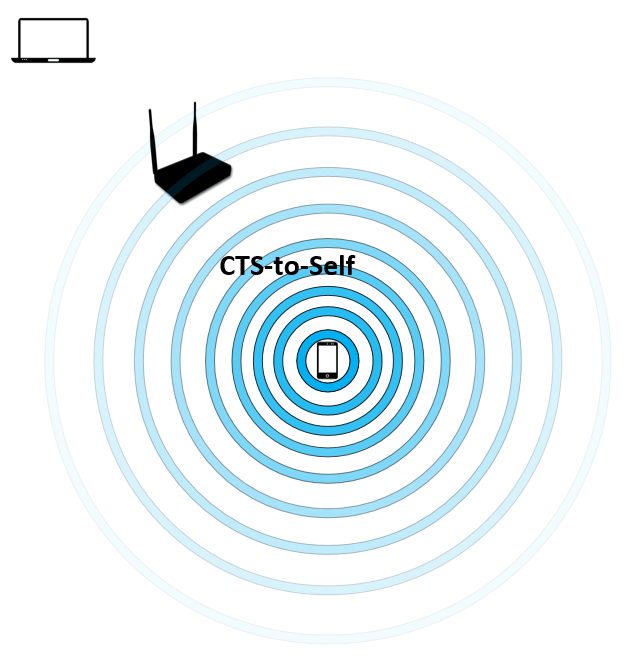
CTS-to-Self is a simpler method of performing NAV distribution. It requires less overhead because only one frame is sent but risks collisions due to clients farther away potentially not being able to decode the CTA frame and set their NAV timers. The duration value in the CTS-to-Self frame is the total time for data, ACK, and two SIFS. This method is best only used by the AP but may be found in use by a station.
The image below shows a mobile phone sending a CTS-to-Self frame. The laptop was unable to decode the frame therefor it does not update its NAV timer.
Conclusion
Understanding these concepts has certainly taken multiple attempts for me, especially some of the logic behind IFS and when each type is used. Creating the graphics and animations in this post will certainly help with the retention of this information. I would encourage anyone to attempt to illustrate these processes in any way to help you see the perspective of a wireless device. I, as one who enjoys playing board games with dice, see all devices in a BSS as rolling dice to see who will take the next turn. While that “player” takes their turn, the others wait and, once the frame exchange is finished, all “players” once again roll their dice again. At times the same player may get to take multiple turns back-to-back, but it averages out over time. It doesn’t take much time for this to happen since we are discussing transmissions taking place over several microseconds which, if you weren’t aware, there are 1 million of in a second.
The introduction of QoS to wireless changed things dramatically for medium contention. Variable and adjustable contention window values allow voice applications to have much higher priority over other traffic types. If we compare this to our analogy, EDCA is like giving each “player” a die with a different number of faces. The players in the voice category roll a D4, video category roll D6s, and players in the best effort and background categories roll D20s.

The background operations of Wi-Fi and how it works is the first step to truly understanding a wireless network. Sure, you don’t need to know some of the fine inner workings in most cases to perform wireless surveys, deploy vendor’s solutions, or even troubleshoot but it is the difference between good and great.
I hope these descriptions and views of wireless contention mechanisms helps you better understand and retain these complicated processes. Most frames mentioned in this post can be found in normal network operations. Capture some and check it out!
Congratulations for making it to the end!
Thanks for reading!
References
IEEE Std 802.11-2007 Section 9.2.3.1
IEEE Std 802.11e-2005
I’m not that much of a internet reader to be honest but your sites really nice, keep
it up! I’ll go ahead and bookmark your site to come back down the road.
Cheers
LikeLike
excellent post and perfect explanation! Thank you for sharing this.
LikeLike