
Wireless networks are often compared to parties or groups of people trying to communicate. In a meeting, one person takes their turn speaking, the others wait until that person is done, then someone else takes the next opportunity to start talking. Wireless devices work the same way. At times they may end up speaking at the same time, but hopefully not too often! The different 802.11 frame exchanges can be thought as the different types of conversations devices “can” have. I compare open system authentication to the common, “Hi, how are you doing?”, “Good, how are you?”, and “Good!” exchange among humans. Imagine there are 10 different types of these quick conversations that end after a matter 2-3 exchanges of words; that is how you can think of 802.11 operations. Some of these exchanges are short enough to remember easily but others reuse the same frames which can lead to confusion.
This post covers information you will be expected to know for the CWNA-107 and CWAP-403 exams. CWAP expects a greater level of understanding of the different types of frame exchanges while the CWNA exam is limited to a few of the exchanges at a higher level. For details on the frame format and contents check out my post 802.11 Frame Types and Formats!
CWNA-107 Objectives covered:
- 3.3 Explain the process used to locate and connect to a WLAN
- 3.3.1 Scanning (active and passive)
- 3.3.2 Authentication
- 3.3.3 Association
- 3.3.4 Open System Authentication
- 3.3.5 802.1X/EAP
- 3.3.6 BSS selection
- 3.5 Explain 802.11 channel access methods
- 3.5.3 RTS/CTS
- 3.5.4 CTS-to-Self
CWAP-403 Objectives covered:
- 6.1 Capture, understand, and analyze BSS discovery and joining frame exchanges
- 6.1.1 BSS discovery
- 6.1.2 802.11 Authentication and Association
- 6.1.3 802.1X/EAP exchanges
- 6.1.4 Pre-shared key authentication
- 6.1.5 Four-way handshake
- 6.1.6 Group key exchange
- 6.1.10 Neighbor discovery
- 6.3 Analyze data frame exchanges
- 6.3.1 Data frames and acknowledgement frames
- 6.3.2 RTS/CTS data frame exchanges
- 6.3.3 QoS data frame exchanges
- 6.3.4 Block Acknowledgement exchanges
- 6.5 Analyze behavior and resolve problems related to MAC layer operations
- 6.5.1 Power Save operations
- 6.5.2 Protection mechanisms
- 6.5.3 Load balancing
- 6.5.4 Band Steering
802.11 State Machine
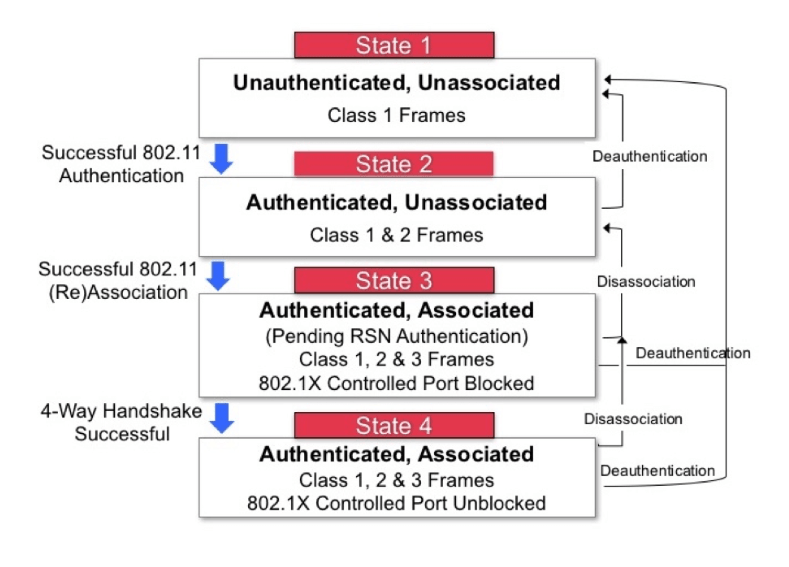
The 802.11 state machine explains the steps a station takes to become authenticated and associated to an AP. The image below shows each of the four “states” as a station makes progress. The arrows to the right show how a station regresses when it becomes disassociated, or deauthenticated by the AP. The following sections cover each of these steps, viewing the exchange of frames between station and AP in detail.
Scanning
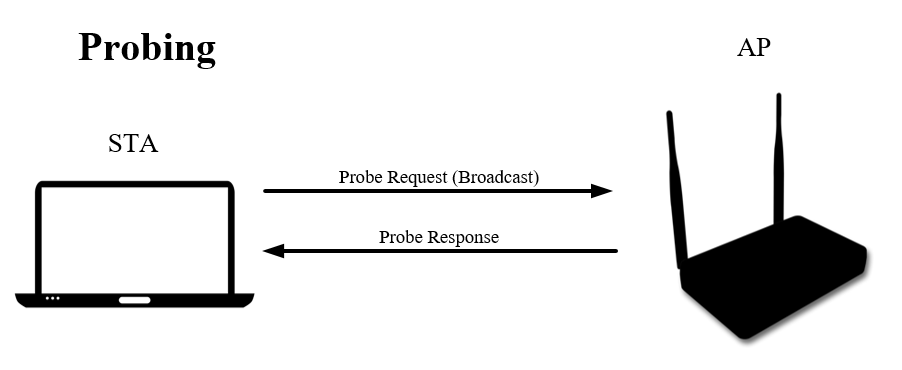
To find APs to associate with, stations perform active or passive scanning. Passive scanning involves listening for beacons sent on each channel and building a list of wireless networks. When a station performs active scanning, it sends probe requests that either specify an SSID or leaves the SSID field empty. An empty SSID field causes all APs within range (on the channel the probe request was sent on) to respond with a probe response frame. If the station includes an SSID in the probe request, only APs that are configured for those SSIDs are expected to respond. After sending probes, the station will wait a pre-determined amount of time, called the ProbeTimer, before moving to the next channel and probing there. Stations will send probe request frames at the lowest data rate for the band they are probing in to reach as many APs as possible. These are 1mbps in 2.4GHz and 6mbps in 5GHz. APs will send probe request frames (and all other management frames) at their lowest mandatory data rate. For the AP this rate can be different for each SSID. Probe requests are broadcasts and do not expect acknowledgement. Probe responses are unicast responses back to the probing station and do expect acknowledgement.

Open System Authentication
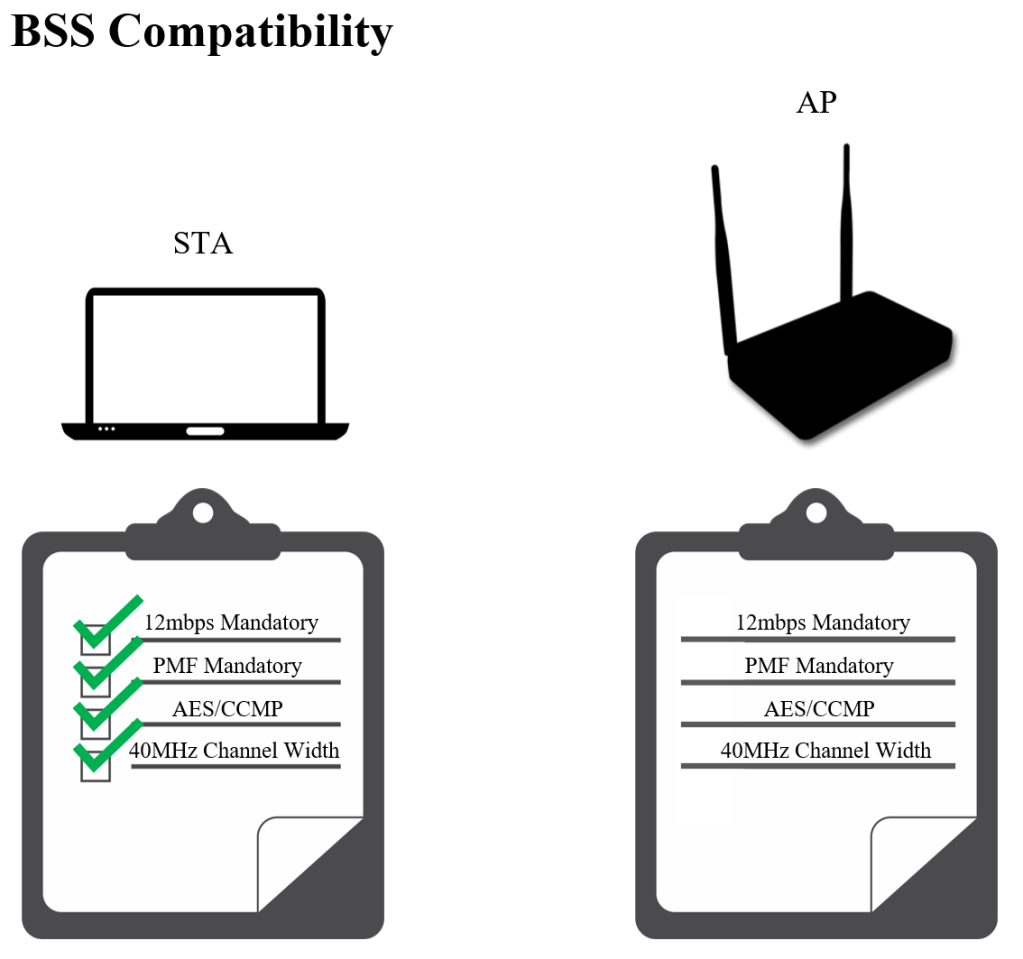
Open system authentication is a simple process to get the station associated with the AP so it can exchange frames to continue through the 802.11 state machine. The process simply checks to make sure the station meets the minimum capabilities to join the operate within the BSS. As shown in the image below, the station knows whether it is compatible by viewing the BSS configuration within the beacon, or probe request, and comparing its own capabilities. This process is completed prior to more advanced authentication methods such as 802.1x/EAP. Open system authentication provides no security or data privacy; WEP can be used in tandem but has been deprecated.
Two authentication frames are used, authentication request and authentication response. As shown below, each of these frames expect an acknowledgement.

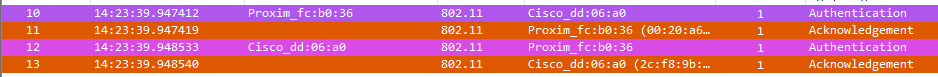
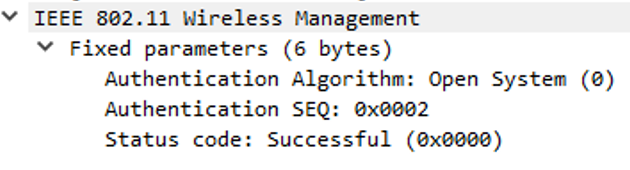
After the open system authentication process is completed, which can be determined by viewing the authentication response frame and seeing “Successful” in the ‘Status Code’ field, the station is in state 2 of the state machine.
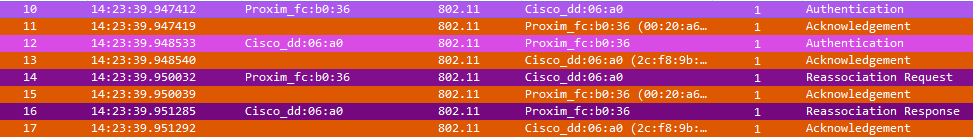
Association
It is up to the station to choose which AP it sends an association request to. Typically, the AP with the best signal strength and SNR that sent a probe response (or beacon) is selected. Stations will send an association request including all the capabilities it has that match those listed in the beacon. This way the AP knows how to best communicate with the station. In the example below, the AP advertises everything it supports (via beacon or probe response) but the station only includes what it supports.
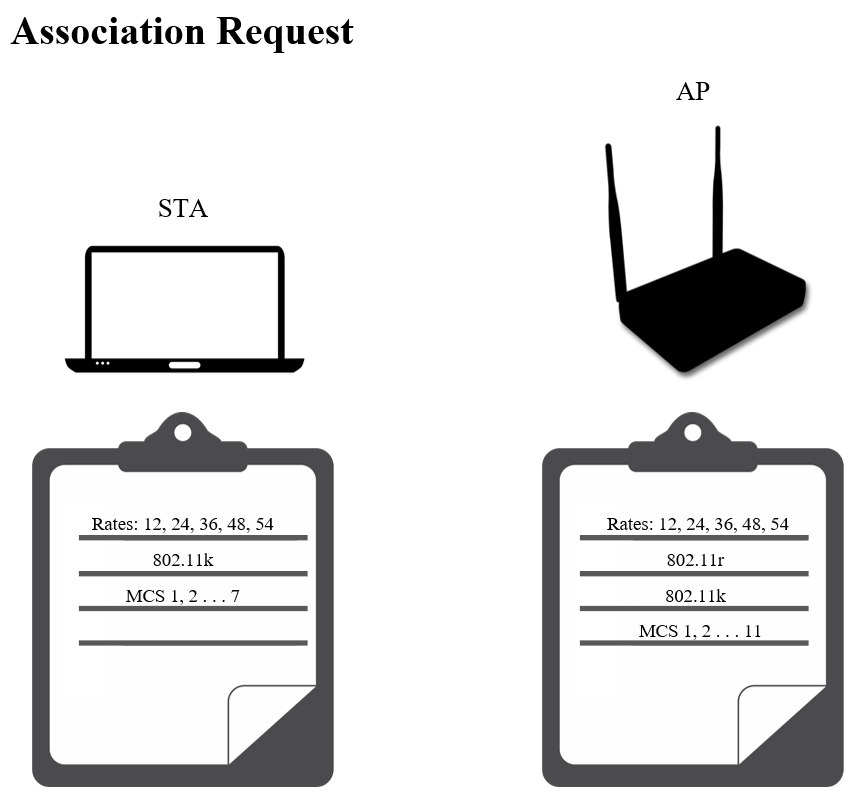
If the open system authentication process is a success, the station will move to the next step of the 802.11 state machine by sending an association request frame. Association request/response frames always expect acknowledgement because they are unicast management frames. The result of this process is the station becoming associated, entering state 3 of the 802.11 state machine, and receiving an association ID (AID) from the access point (AP).

802.1x/EAP Exchange
When the SSID security is set to 802.1x, the station will communicate with the authentication server through the access point to become authenticated. There are two virtual ports maintained by the AP, controlled and uncontrolled. Until the station receives the “Success” EAP Frame, traffic other than EAP is blocked through the controlled port. After the authentication is successful, the AP will unblock the controlled port to allow the station to send/receive traffic.
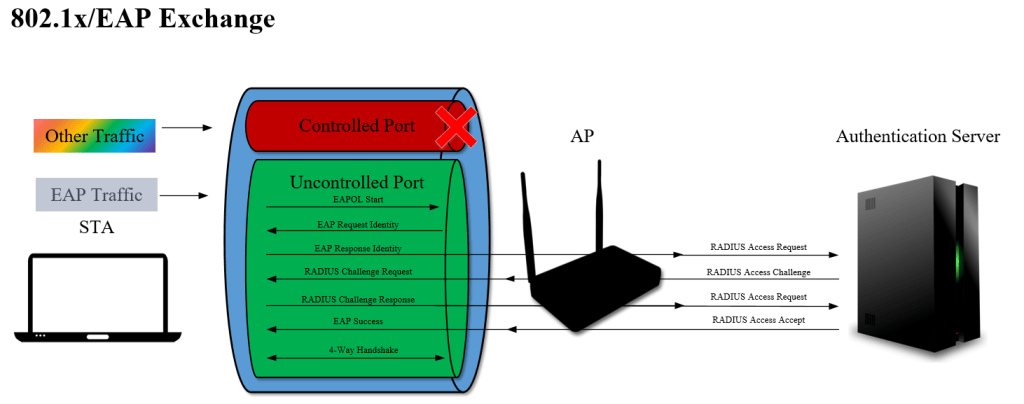
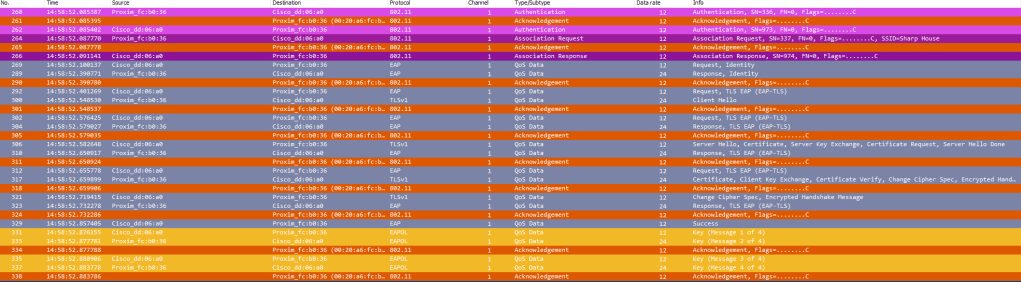
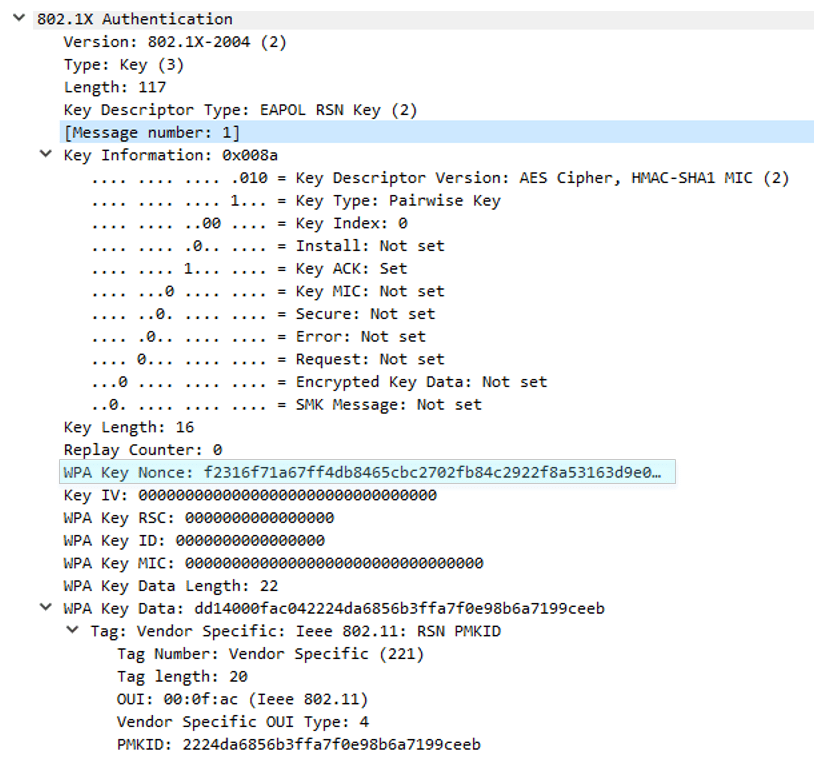
During the exchange, the station and AP generate a pairwise master key (PMK) that is later used during the four-way handshake to derive the pairwise transient key (PTK). After the exchange is successful, the client now has a pairwise master key security association (PMKSA) with the AP. The AP gives the station a PMKID that is unique for that station. The 802.11-2016 standard states that stations and APs can save multiple PMKSAs. Saving these enables faster roaming between APs by roaming back to an AP or by pre-authenticating with the next. When a station roams to an AP where it previously had a PMKSA, it will include its PMKID in the RSN information element of the reassociation request frame to skip the 802.1x/EAP authentication process (if the PMKID is still valid); this reduces roaming time. The 802.11-2016 standard states: “The context resulting from a successful IEEE 802.1X authentication exchange between the peer and Authentication Server (AS) or from a pre-shared key (PSK).”
Four-way Handshake
The four-way handshake is used to derive both the PTK and GTK which are used to encrypt unicast and multi/broadcast data. After the station completes open system authentication and association, the next step in a PSK-protected wireless network is to complete the four-way handshake process so it can start sending protected (encrypted) data frames. Four frames are exchanged, each of which are acknowledged by the recipient. These frames are sent as normal data frames in legacy networks or QoS data frames.
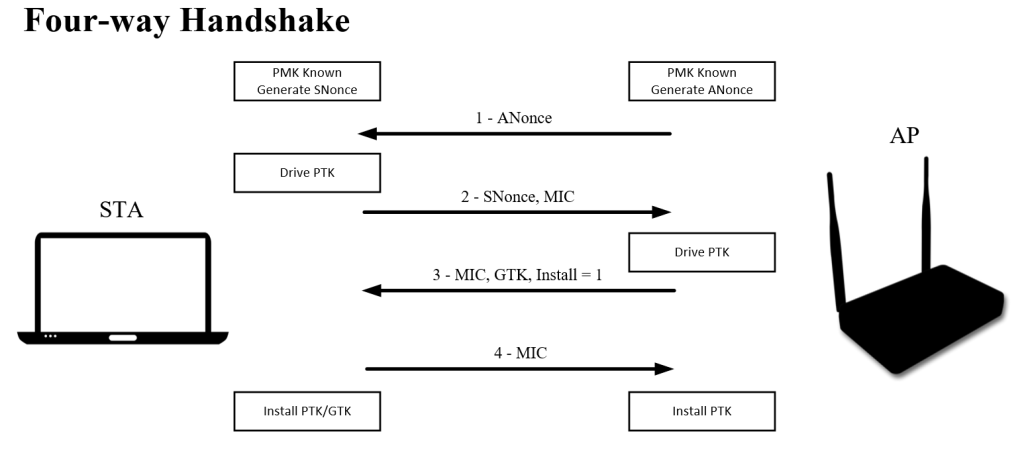
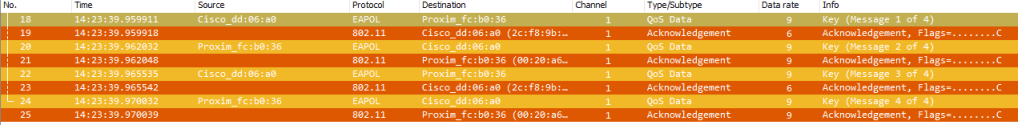
Message 1
The station generates a random number called an SNonce (supplicant nonce) in the background. The AP generates a random number called an ANonce (authenticator nonce), puts it into an EAPOL-Key frame, and sends it to the station. The station uses the PMK (derived from the PSK or EAP method), ANonce, SNonce, and MAC addresses to generate the PTK that is used to encrypt unicast traffic.
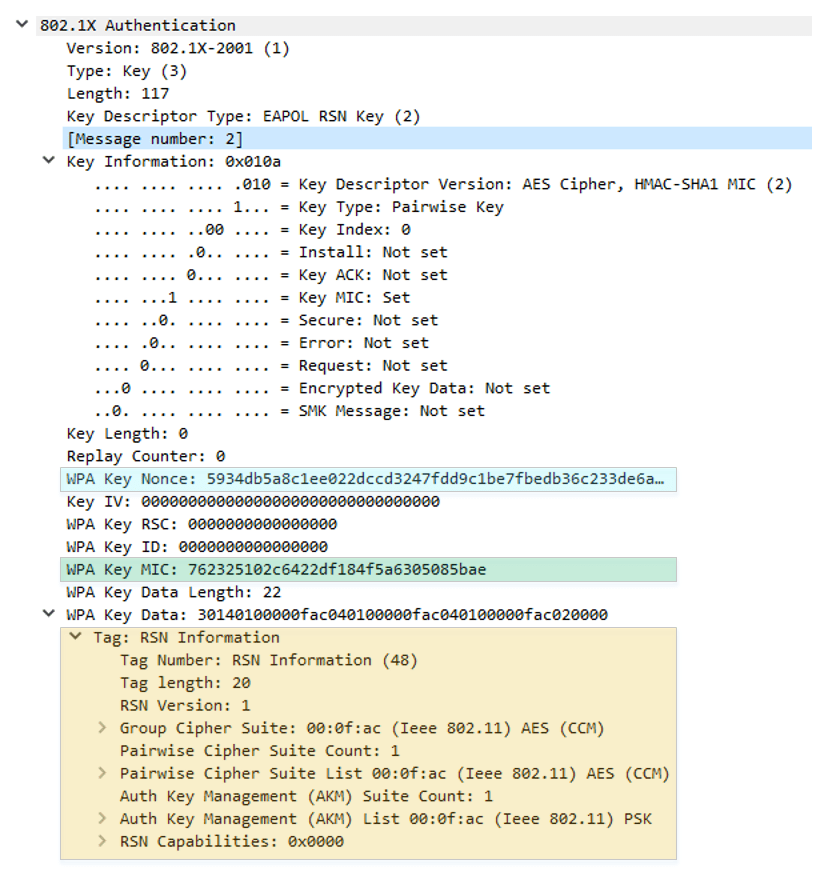
Message 2
The station sends its SNonce to the AP in an EAPOL-Key frame. The AP now has all the same information which it uses to generate the same PTK to encrypt unicast traffic. The station also includes a message integrity code (MIC) along with the RSN information element to present its capabilities.
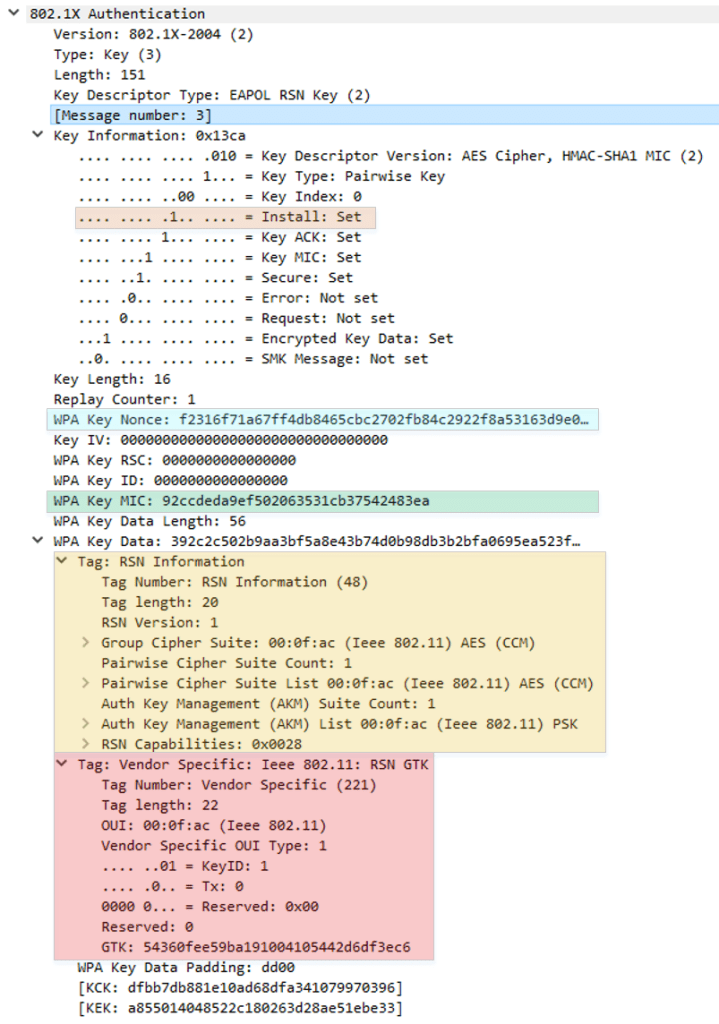
Message 3
The AP sends the station its ANonce, RSN information element, and a MIC in an EAPOL-Key frame. GTK is created by the AP using GMK. The GTK is delivered to the station; this is encrypted using the established PTK. The Install field is set to 1 to notify the station to install the PTK.
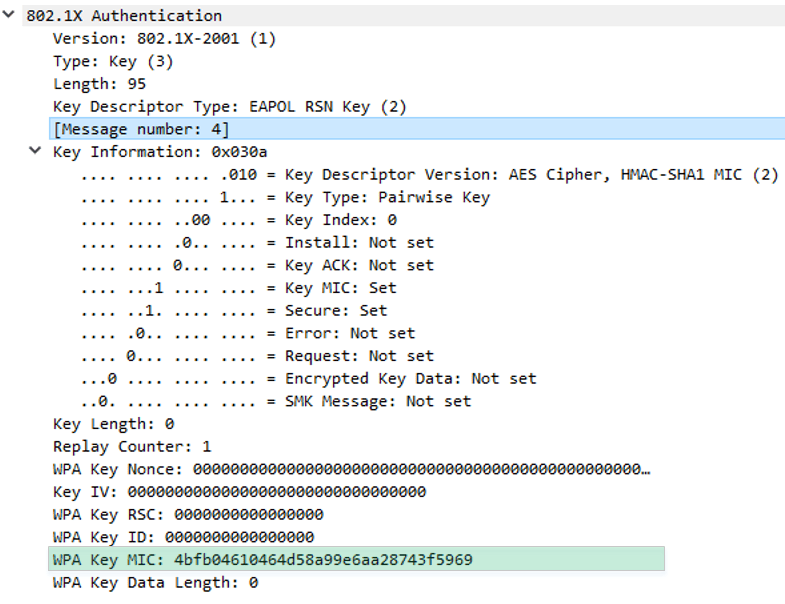
Message 4
The station sends a confirmation and MIC to the AP within an EAPOL-Key frame.
Following the four-way handshake process, the station now has a robust security network association (RSNA) or pairwise transient key security association (PTKSA) and is at the fourth and final state of the 802.11 state machine.
Dissasociation and Deauthentication
Disassociate and Deauthenticate frames are management frames. They are notifications and do not expect acknowledgement. Clients may disassociate prior to powering off. APs may disassociate clients for various reasons including failure to properly authenticate, for load balancing or timeout reasons, entering a state of maintenance, etc. The 802.11-2016 standard includes a list of reason codes. When a station is disassociated it still maintains its authentication. This makes it easier for the client to associate again in the future. Deauthentication frames are used to reset the state machine back to state 1 for an associated client. The authentication process takes place prior to association therefor, if a station is deauthenticated, it is also disassociated. The body of Dissassociate and Deauthentication frames includes a reason code explaining why the frame was sent.

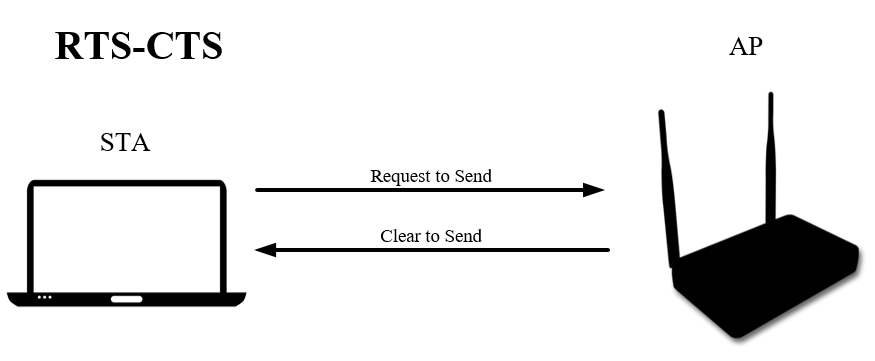
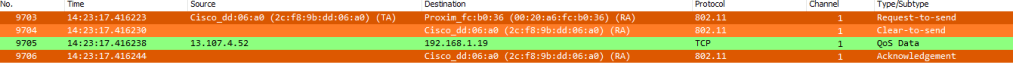
RTS-CTS
Request to send (RTS) and clear to send (CTS) frames are exchanged between station and AP to inform all stations in the BSS that a station will be transmitting for an amount of time found in the duration field of the frame header. The station sends the RTS message to the AP requesting to reserve the wireless medium for the amount of time (in microseconds) in t he duration field. The AP then responds with a CTA frame. These frames don’t expect an acknowledgement because they are unicast control frames. The station does not have control of the medium until the AP responds.
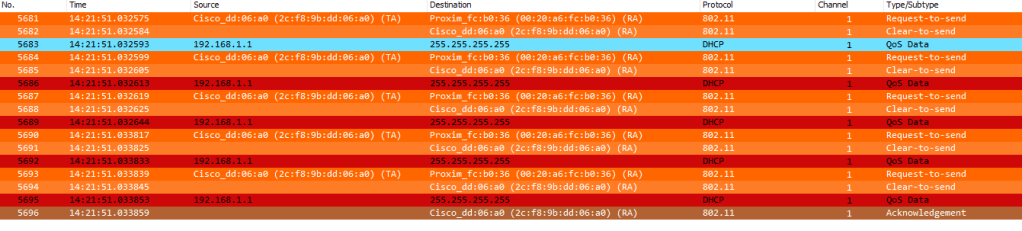
In the example below 192.168.1.1 is attempting to complete the DHCP process but the AP never receives an ACK from the station. This is why (based on my colorization rules within Wireshark) the first QoS Data frame below shows blue but the ones following that are retransmits are red. The AP, in this example, lowers the data rate at which it transmits the QoS Data frame in an effort to successfully deliver the frame (and stabilize the connection). The exchange ends after the AP finally receives an ACK.
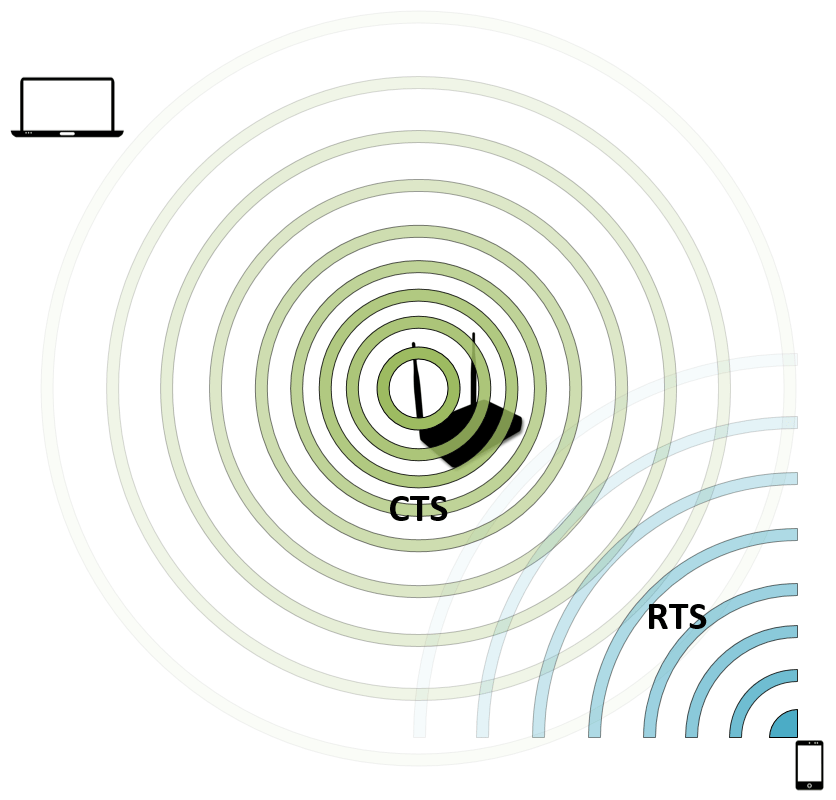
CTS-to-Self
CTS-to-Self is a simpler method of advertising a station is going to transmit for a set amount of time. It requires less overhead because only one frame is sent but risks collisions due to clients farther away potentially not being able to decode the CTA frame and set their NAV timers. This method is best only used by the AP but may be found in use by a station.
The image below shows a mobile phone sending a CTS-to-Self frame. The laptop was unable to decode the frame therefor it does not update its NAV timer.
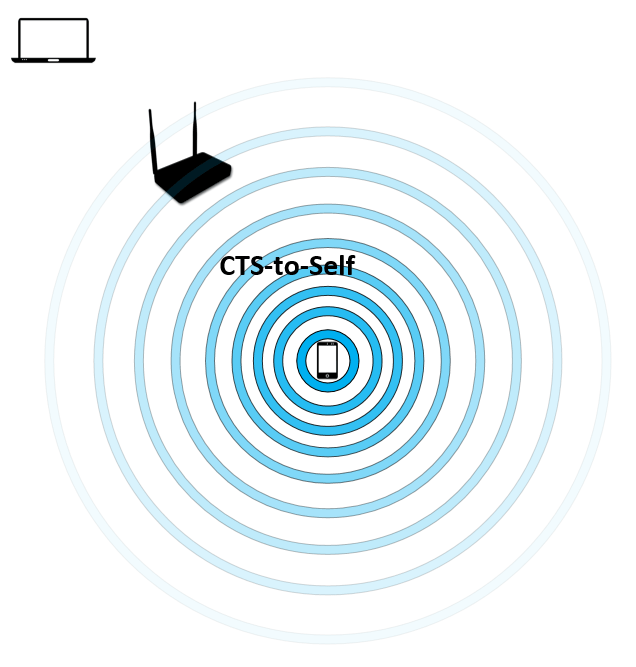
A frame capture will show a station sending CTS frames with its own MAC address in the receiver address (RA) field.
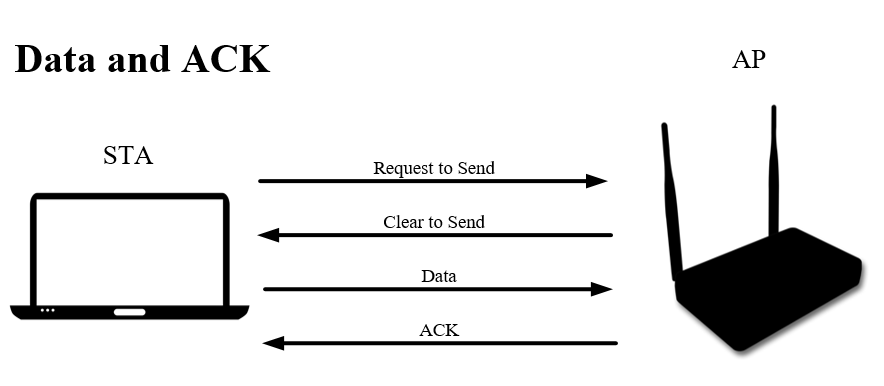
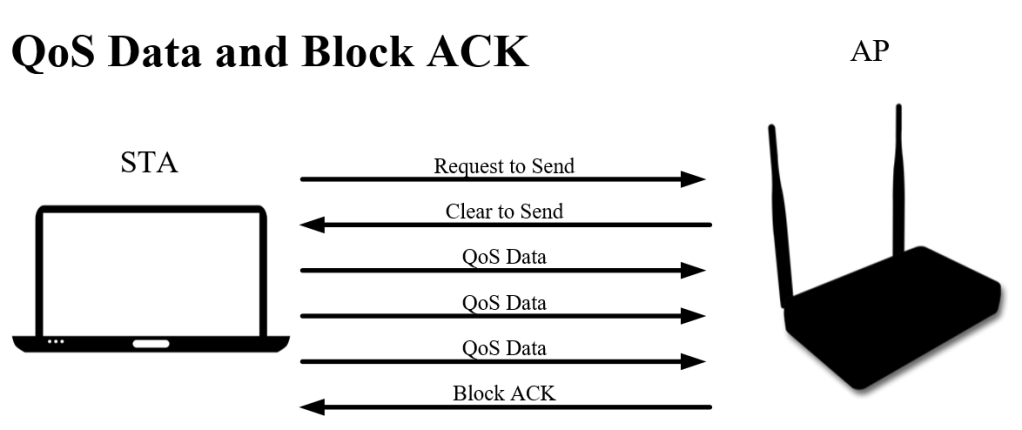
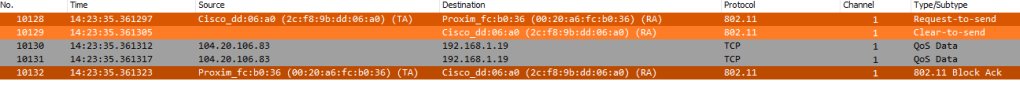
Data and Acknowledgement
Data frames contain layer 3-7 information in the body of the frame. All unicast data frames expect an ACK and will otherwise be retransmitted. QoS data frames are always used when both stations support it. For QoS frame exchanges, Block Acknowledgements can be used to allow a station to send a burst of frames and only expect a single ACK called a Block ACK.
What frames expect ACKs?
Per the 802.11-2016 standard, the following frame types/subtypes should be acknowledged by the recipient:
- All unicast data frames
- All unicast management frames
- All PS-Poll control frames (not other unicast control frames)
Power Save
PS-Poll
Prior to 802.11e-2005, STAs used the PS-Poll control frame to request buffered frames from the AP after waking up. Stations include listen intervals in association request frames to indicate how often they will wake up to receive frames buffered on the AP.

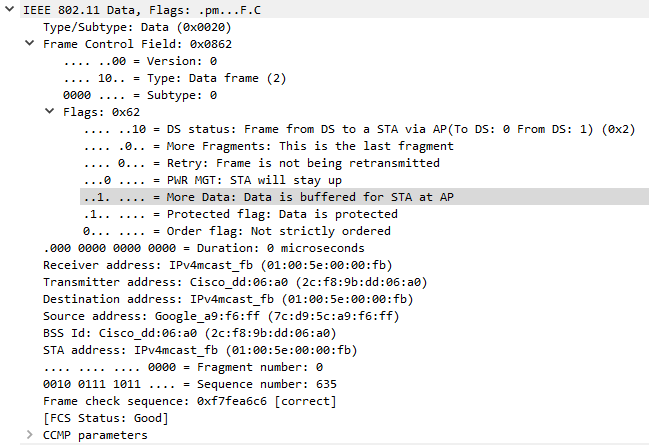
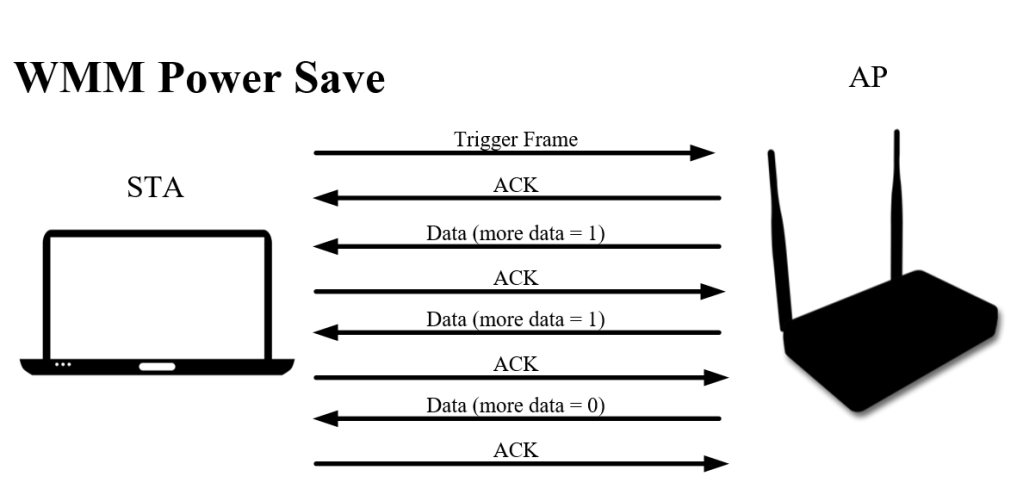
WMM Power Save
802.11e-2005 introduced WMM power save. This made the buffered data retrieval process much more efficient by enabling any frame to act as a trigger frame. When the AP sees that the station is awake it will send buffered frames in a single contention window (TXOP Burst).
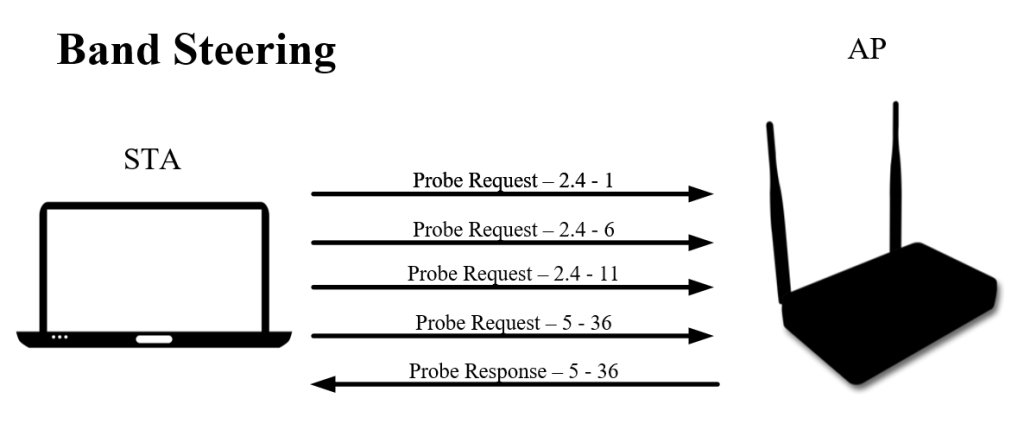
Band Steering
Band steering is used to assist stations in prioritizing 5GHz when the SSID is broadcasted on both 2.4 and 5GHz bands. It works by delaying response to probe requests on 2.4GHz. The AP won’t leave the client stranded though, each vendor implements band steering differently as it isn’t defined in the 802.11-2016 standard. Meraki’s documentation on band steering states “If the AP hears a probe request from a wireless client on the 2.4GHz band while band steering is enabled, it only responds if it has not heard anything on the 5GHz band from that same client in the last 60 seconds.” Cisco doesn’t share the amount of time used in their band steering feature on traditional controllers (AireOS).
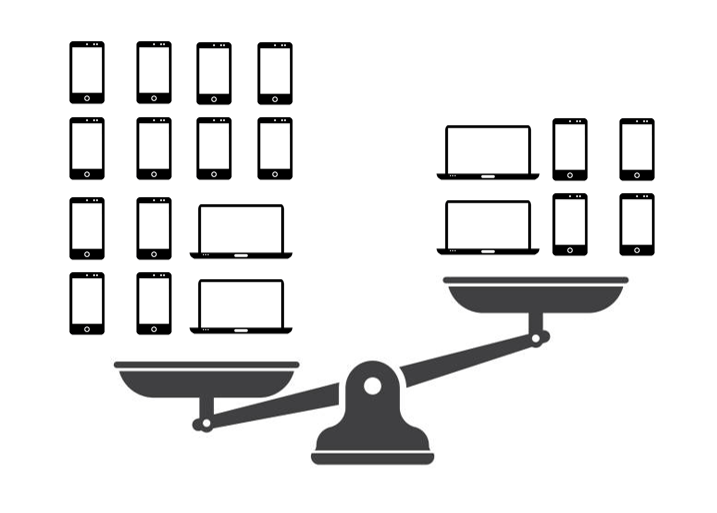
Load Balancing
Load balancing was introduced in 802.11v to better service clients by better distributing the load of clients among APs in an area. This avoids too many clients connecting to a single AP when a nearby AP has fewer clients and could better service the stations. Many vendors have their own implementation of 802.11v and do not share the algorithms they use. Notably, Meraki has their “Client balancing” enabled by default in the pre-built RF Profiles and on all new RF Profiles. Load balancing in Meraki works by the AP not sending association responses to association request frames. I have seen this cause more harm than good in every environment its enabled in.

Example PCAP
Attached is a PCAP file that you can use to apply filters to view the frames for yourself to better understand the frame format and values. The frames that can be found include: association request/response, authentication request/response, probe request/response, 4-way handshake, RTS/CTS, QoS and simple data frames, and more! It also includes captures of the data frames for inspection of layer 3-7.
Basic Information
SSID: HowIWiFi
PSK: CWAPnotes123
STA: 00:20:A6:FC:B0:36
AP: 2C:F8:9B:DD:06:A0
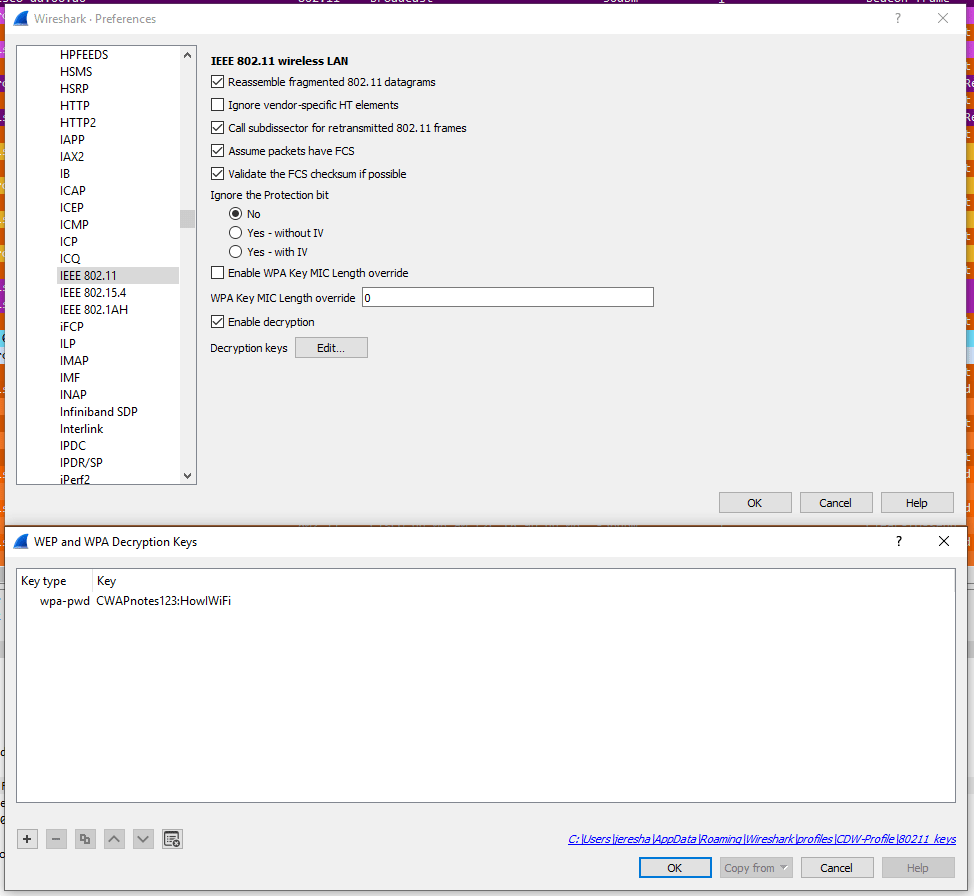
To decrypt the data frames in this capture, open preferences, select IEEE 802.11, select “Edit…” next to Decryption keys, and enter the PSK and SSID as shown below.
Below is a list of filters you can apply and the types of frames that will be shown.
| Filter | Frames |
| frame.number >= 9250 && frame.number <=9274 | Disassociation, Deauthentication, Authentication, Association Request/Response, 4-way handshake (EAPOL), ACKs |
| frame.number == 4505 || frame.number == 4507 | Station using action frame to request 802.11k neighbor report and AP responding with report. |
| (wlan.fc.pwrmgt == 1) && (wlan.fc.type_subtype == 0x0024) | Station using null data frame to notify the AP that it is going to sleep. |
| wlan.fc.type_subtype == 0x000a | Station sends disassociation frame to AP with “STA is leaving BSS” reason code. AP sends disassociation frame to STA with “Unknown” reason code. |
| wlan.fc.retry == 1 | Shows number of times a frame had to be retransmitted. 2.4% of frames in capture. |
| wlan.fc.type_subtype == 0x000c | AP sends deauthentication frames to STA with reason codes “Unknown” and “Class 3 frame received from nonassociated STA” meaning that the STA transmitted frames prior to association. |
| wlan.fc.type_subtype == 0x0005 || wlan.fc.type_subtype == 0x0004 | Shows all probe requests and probe responses. |
| frame.number >= 15946 && frame.number <= 15949 | AP sends RTS to STA, AP sends CTS with RA as itself to indicate that it is clear to transmit frames, AP sends QoS data frame to STA, and STA sends a Block ACK to confirm receipt. |
Conclusion
Although there are many different frame exchange processes, many are short and have similarities. Performing protocol analysis and watching devices join a BSS live is the best way to understand wireless communications. Although frames are sometimes missed and can appear out of order within Wireshark, you can typically get an idea of the basic back-and-forth exchanges between two stations or station and AP. Be aware of a few topics not covered in this post including: aggregate frames (A-MSDU and A-MPDU), block ACK in detail, and the exchanges used to generate beamforming matrices.
I hope these simplified explanations and graphics, Wireshark screenshots, and attached PCAPs help you better understand the different types of frame exchanges!
References
IEEE 802.11-2016 Standard
https://blogs.arubanetworks.com/industries/understanding-802-11-state-machine/
https://www.cwnp.com/forums/posts?postNum=304169
https://documentation.meraki.com/MR/Radio_Settings/Band_Steering_Overview